Google says 90 zero-days exploited in 2025 as commercial vendor activity grows
Commercial surveillance vendors are increasingly leading the charge in exploiting zero-day vulnerabilities according to a new report.
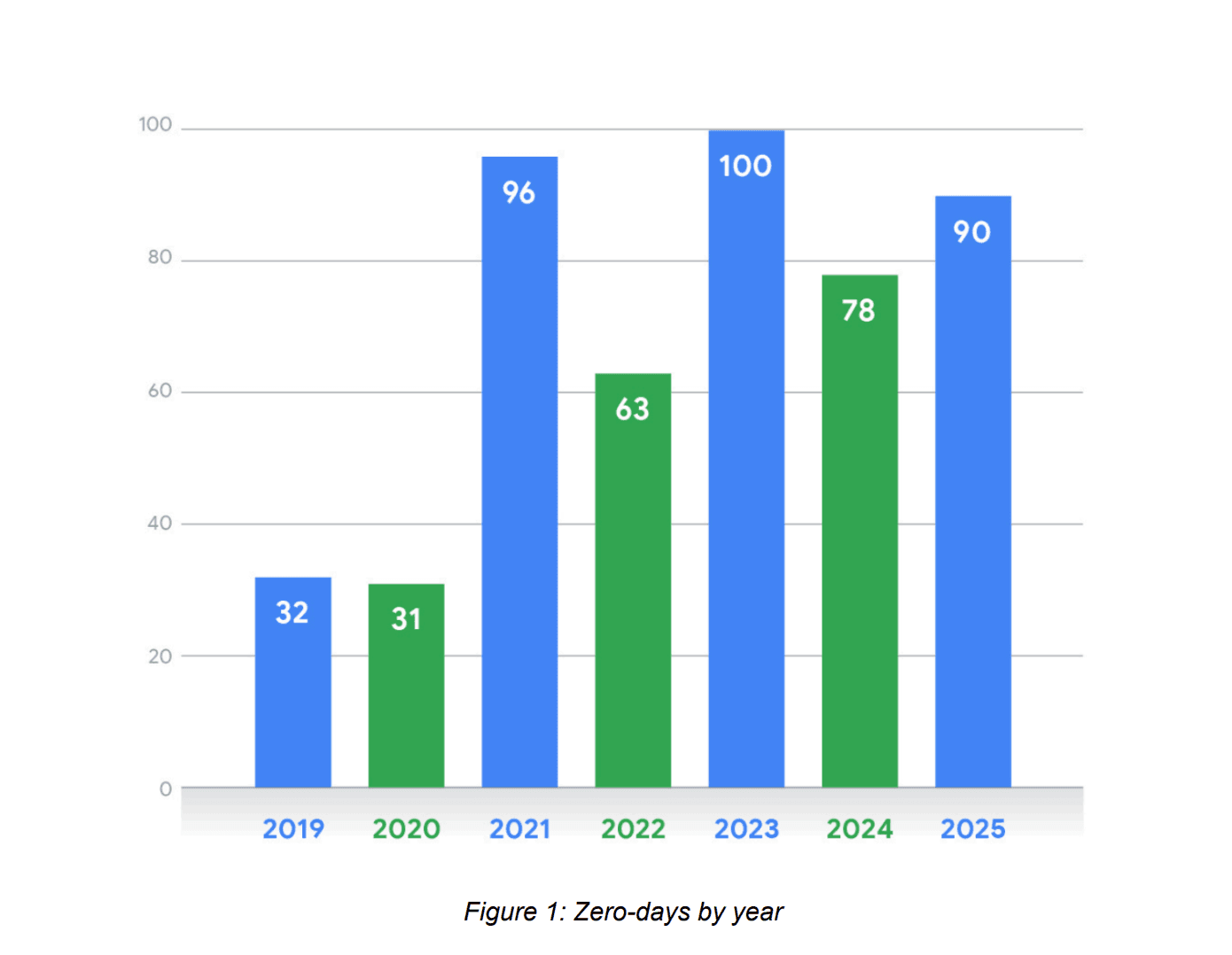
Google Threat Intelligence Group said it tracked 90 zero-day vulnerabilities that were exploited by a variety of actors last year, surpassing the 78 that were used by threat actors in 2024. The company defines zero-days as vulnerabilities that were maliciously exploited in the wild before a patch could be released publicly.
Of the 90 zero-days tracked last year, GTIG was able to directly attribute exploitation for 42 of them — finding that 18 were either definitively or likely used by commercial surveillance vendors. Fifteen were deployed or likely deployed by state-sponsored espionage groups based in China, Russia, the UAE and other countries.
The two groups focused their efforts on different technologies, with state-sponsored groups prioritizing edge devices and security appliances like routers or firewalls that enable access to an organization’s network.
Commercial surveillance vendors primarily targeted mobile devices and browsers — aiming to sell tools that allow for the breach of personal technology. Mobile device zero-days have fluctuated wildly over the last three years, dropping from 17 to 9 between 2023 and 2024, and then rebounding to 15 in 2025.
Microsoft technology had the largest number of zero-days followed by Google and Apple, according to the report.
Nation-state targeting
Throughout 2025, government agencies across the U.S. and Europe raised alarms about zero-day vulnerabilities in security tools from companies like Ivanti, Cisco, Fortinet and others.
The GTIG report focuses on zero-days developed by espionage groups based in the People’s Republic of China, noting that in comparison to other state-backed actors, Chinese groups “remained the most prolific users of zero-day vulnerabilities in 2025.”
The groups “continued to focus heavily on security appliances and edge devices to maintain persistent access to strategic targets.”
Edge devices have been repeatedly targeted by state-backed groups because many routers, switches and security appliances sit on the perimeter of an organization's infrastructure and typically lack endpoint detection and response security coverage — serving as a blind spot for defenders.
One month ago, U.S. officials ordered all federal civilian agencies to remove edge devices that no longer receive vendor updates to firmware or other security patches.
GTIG noted its previous reporting on a campaign involving the Brickstorm malware that was attributed to Chinese state-backed groups. The researchers warned that the campaign marked a “new paradigm for zero-day exploitation where data theft has the potential to enable long-term zero-day development.”
“Instead of just exfiltrating sensitive client data, the threat actors targeted intellectual property from the victim companies, potentially including source code and proprietary development documents,” the researchers said.
“This IP could be used to discover new vulnerabilities in the vendor's software, not only posing a threat to the victims themselves but also to victims’ downstream customers.”
Key examples of Chinese exploitation included Juniper Networks’ CVE-2025-21590 and Ivanti’s CVE-2025-0282. The report adds that there have been shifts in Chinese behavior regarding zero-days.
Chinese groups typically provided zero-days to a small group of well-resourced threat actors but now “an increasing number of activity clusters are exploiting vulnerabilities closer to public disclosure, indicating that PRC-nexus espionage operators have potentially reduced the time to both develop exploits and distribute them among otherwise separate groups.”
Commercial vendors and criminals
Mobile operating system exploitation saw increases in the number of zero-days last year in part because commercial surveillance vendors created exploit chains involving three or more vulnerabilities.
Google has long warned of the increasing role commercial surveillance vendors are playing in the zero-day industry, highlighting the work of companies like Intellexa in providing “extremely capable spyware to high paying customers” that “erode civil liberties and human rights.”
“This is reflected not only in the gradual proliferation of exploit code targeting specific vulnerabilities, but also by the shrinking gap between the public disclosure of n-day vulnerabilities and their widespread exploitation by multiple groups,” they wrote.
Boris Cipot, senior security engineer at security firm Black Duck, said that the exploits and capabilities outlined in the report are becoming more widely accessible and less confined to traditional intelligence services.
When asked who the end user is for zero-days developed by commercial vendors, Clement Lecigne, security engineer at GTIG, said most of the companies they track “primarily sell to nation-states.”
GTIG also tracked nine zero-days developed and exploited by financially-motivated hackers, including a headline-grabbing bug impacting Oracle E-Business Suite that was developed by a hacker claiming affiliation with the Clop extortion cybercriminal group. The group sent extortion emails to hundreds of organizations after exploiting CVE-2025-61882 and CVE-2025-61884 in August 2025.
The researchers also found overlaps between state-sponsored groups and financially-motivated actors, noting that it saw hackers connected to Russia-based group Evil Corp using CVE-2025-8088 to distribute malware.
The same bug was also used in attacks by the RomCom group — which has conducted both financially-motivated attacks and espionage operations.
GTIG senior vulnerability intelligence analyst Casey Charrier said the new landscape “is largely defined by expanded access to zero-day capabilities, interwoven with the drastic movement we’ve seen over multiple years towards exploitation of more diversified vendors and products, a shift from which threat actors are certainly seeing success.”
“The struggle to protect highly privileged edge devices remains a critical gap; security flaws in these high-value assets continue to serve as leverage for wide-scale exploitation,” Charrier said.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.